 Hello,
Hello,
Over the last several decades the terms information security and cybersecurity have become conflated to the extent that they’re used interchangeably. Information security is cybersecurity is information security. For sources that do identify a difference between the two, it’s often two sides of the same coin: Information security speaks to the attributes of security while cybersecurity is about implementing mechanisms to achieve those attributes.
In practice, however, cybersecurity has evolved to embody a specific set of cultural precepts that pervade the contemporary cybersecurity community. On a macro level, these include:
- The idea that multiple, concentric perimeters comprising the right tools and products, compliant with the right frameworks, and managed by the right people can stop most, if not all attacks;
- A concept in which information reliably inherits protections from those applied to the devices and networks on which it is managed; and
- A belief that operational friction is an expected and acceptable price to pay for the implementation of security technologies.
Put in terms of the NIST Cybersecurity Framework, contemporary cybersecurity is focused on the Identify, Detect, and Protect functions, less so on the Respond and Recover functions.
Unfortunately, these perspectives fail to address the concerns of the larger operational community. Operational leaders intuitively understand not only that their organizations operate in a hostile cyberspace, but that their key imperatives are to continue to operate in that environment and, in the event that an attack is successful, to be able to resume operations as soon as possible. In NIST terms, operational leaders are focused on responding and recovering.
This divergence in perspective implies a need for a taxonomical revision, one where information security holds the top rank and breaks down into two top level subordinate groups, cybersecurity and resilience:
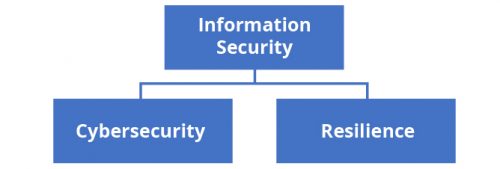
Cybersecurity is concerned with defense and attempting to prevent or mitigate the realization of risks. Resilience is a discipline concerned with ensuring that the organization is able to continue its mission despite ongoing malicious and inadvertent threats and successful attacks, and/or is able to recover and resume operations with a minimum of lost time and opportunity.
Where cybersecurity reflects the perspectives and priorities of the security community, resilience reflects the needs and requirements of the business operations served by the that community. They’re inherently complementary; organizations should do what they can to prevent information security risks from being realized, but in the event that the risks are realized, being resilient blunts the impact and enables continued operations despite an incident.
For one example, an attacker might successfully penetrate an organization’s cybersecurity defenses and exfiltrate sensitive information. However, if the organization’s information is pervasively encrypted, the attacker retrieves nothing of value. (Indeed, this type of outcome might result in an improvement in the overall community’s information security posture: An attacker that has dedicated significant time and resources toward breaching defenses, only to achieve a negative return on investment is less able to prosecute attacks on other targets.)
In another example, an attacker might initiate ransomware or another denial of availability attack. If the targeted organization adopted an immutable storage solution, many of the files the attacker sought to infect might not be susceptible. Similarly, a combination of decentralization and continuous backup technologies both raises costs and effort unacceptably for an attacker and enables the victim organization to recover quickly enough to minimize an incentive to pay the ransom.
Happily, resilience as both a concept and a policy is about to go mainstream. White House and cabinet level organizations have realized how resilience complements cybersecurity, and the information security community can look forward to new guidance emphasizing resilience as a discipline and a requirement.
Build it right, America.
![]()
Adam Firestone
Editor-in-Chief


Leave a Comment