The internet has become vital to nearly every aspect of modern life. People depend on websites and applications for banking, shopping, education, remote work, healthcare, and everyday communication.
However, one of the biggest threats to online reliability is the Distributed Denial-of-Service (DDoS) attack. A DDoS attack floods a targeted website with excessive fake requests, overwhelming its servers and preventing legitimate users from gaining access.
To defend against this, many organizations now rely on DDoS mitigation service that filter harmful traffic before it can cause disruption.
Why Traditional Methods Fall Short
Attackers today use vast networks of compromised devices—such as computers, smartphones, cameras, and IoT gadgets—to launch their assaults. These cyber threat can originate simultaneously from thousands of sources around the world.
Legacy protection tools often fail to respond in time. They typically detect an attack only after service slowdowns or outages occur. Furthermore, they depend heavily on manually created rules, which can’t adapt quickly enough as attackers evolve their tactics.
Understanding the Root Causes of the Problem
Old systems struggle against modern DDoS attacks for several key reasons:
1. Detection occurs too late.
Older systems usually monitor traffic only after it reaches centralized data centers—by then, the damage is already done causing significant problems.
2. Attacks are larger than ever.
Massive botnets generate overwhelming amounts of traffic that exceed what any single server can process.
3. No real-time learning.
Legacy tools can’t distinguish normal user behavior from anomalies until something has already gone wrong.
4. Manual rule updates and filters are too slow.
Security teams must write new filters by hand, which is impractical during fast-moving attacks.
5. Limited points of protection.
Centralized systems guard only a few locations, while attackers exploit distributed networks across the globe.
These weaknesses make a strong case for a faster, smarter, and more distributed form of protection—one that combines Artificial Intelligence (AI) and Edge Computing.
Using AI and Edge Computing Together Make Sense
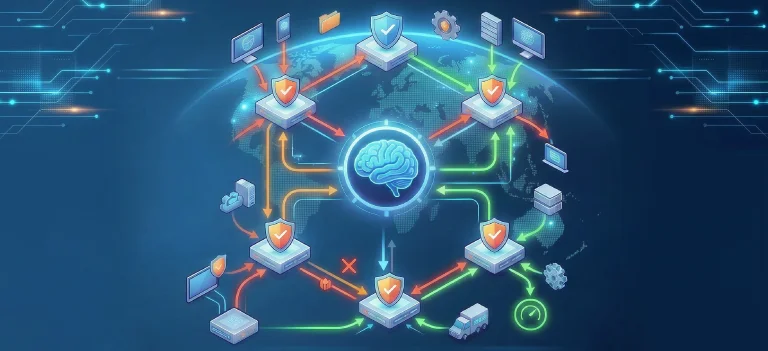
Together, AI and edge computing create a dynamic defense model. AI continuously analyzes network activity to learn what “normal” looks like, while edge computing places security checkpoints closer to users—reducing latency and improving response speed.
Edge computing, in simple terms, involves deploying small servers in multiple geographic locations. These servers handle traffic locally instead of sending everything to a central data center.
AI, meanwhile, monitors and learns from traffic trends. It can spot unusual spikes or suspicious behavior in real time, often before users experience any slowdown.
How AI and Edge Computing Approach Stops DDoS Attacks
1. Real-time traffic inspection.
Edge servers check and filter traffic immediately, blocking malicious requests before they hit the main infrastructure.
2. Adaptive AI learning.
AI studies behavior patterns—how users engage with the site, typical traffic volumes, device types, and time-of-day activity—to identify anything unusual.
3. Autonomous threat detection.
AI can recognize and respond to new attack patterns on its own, reducing dependence on manual configurations.
Collaborative defense.
Edge servers communicate globally, sharing insights so that once an attack is detected at one point, others can prepare instantly.
Businesses Can Implement AI and Edge Computing in Daily Operations
Organizations can gradually integrate AI and edge computing into their cybersecurity strategies:
Step 1. Deploy edge locations through cloud providers or technology partners.
Step 2. Train AI models with real network traffic to establish a clear baseline of normal activity.
Step 3. Route all traffic through edge servers so malicious data is intercepted early.
Step 4. Continuously update AI models to reflect evolving threats and usage patterns.
Step 5. Create a rapid response plan that defines immediate actions when AI flags abnormal traffic.
Conclusion
DDoS aAIttacks are growing faster, larger, and more sophisticated—outpacing traditional defenses. By combining AI’s learning capabilities with the speed and reach of edge computing, organizations can detect anomalies earlier, block malicious traffic instantly, and maintain service continuity even under heavy attack.
This integrated approach represents the next generation of DDoS protection: proactive, intelligent, and globally resilient. This method is novel, practical and robust.
Tags: AI, Botnet, Cyber Attacks, DDoS, DDoS Attacks, Edge Computing