Cloud
RSAC 2026 Conference
Author(s):
March 23-26, 2026 | 8:00 AM – 3:30 PM (PDT) Moscone Center747 Howard Street | San Francisco, California 94103 The Power of Community Starts with You Ideas become breakthroughs when shared. Challenges become opportunities when … Read more
INTERFACE Portland 2026
Author(s):
INTERFACE Portland 2026 Oregon Convention Center | Portland Ballroom 777 NE Martin Luther King, Jr. Boulevard | Portland, Oregon 97232 IT Infrastructure is constantly changing, bringing more new challenges with it every day. From ransomware … Read more
SANS DC Metro March 2026
Author(s):
March 2-7, 2026 | In Person & Virtual (EST) Hilton Arlington Rosslyn The Key & Virtual 1900 Fort Myer Drive | Arlington, Virginia 22209 Unleash Elite Potential. Transform Your Career. The future of cybersecurity starts … Read more
6 Data-Backed Predictions for Cybersecurity in 2023
Author(s):
Oscar Collins, Editor-in-Chief, Modded
Changes in technology happen rapidly. Innovations emerge as people and companies conduct business every day. Tech can be a significant benefit or a detriment when cybercriminals take advantage of innocent people and attack their vulnerabilities. … Read more
Benefits of Using Cloud Security Posture Management (CSPM)
Author(s):
Erik Kaminski, Author,
Cloud computing has been revolutionizing the IT industry in the last couple of years. As a relatively new technology, cloud computing has changed the way both companies and individuals go about handling the required resources. … Read more
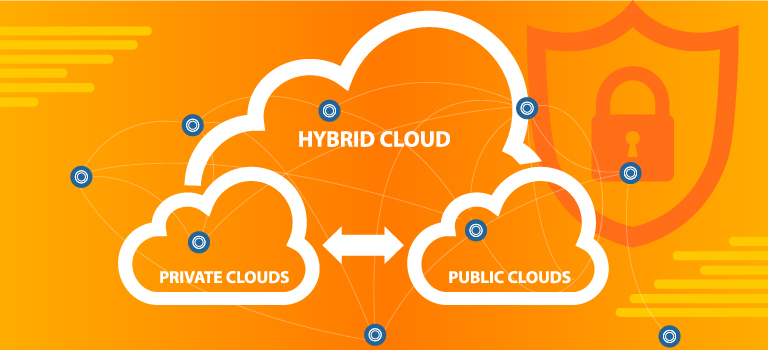
Addressing the Challenges of Securing Hybrid Cloud Access: What You Need to Know
Author(s):
Joseph Carson, Chief Security Scientist & Advisory CISO, Delinea
For a growing number of companies, a blend of public cloud services, private clouds, and on-premises infrastructure offer the best solution to the benefits and limitations of each. Cloud adoption is growing, and the past … Read more
Cybersecurity & Your Business
How Can Organizations Prioritize Data Privacy Through Encryption?
Author(s):
Waqas S, Cybersecurity Journalist, DontSpoof
Rapid technological advancements have transcended data in value, making it highly significant to individuals and organizations. With that being said, despite the many regulations protecting data rights, such as the General Data Protection Regulation (GDPR), … Read more
Securing Your Data
The Importance of Protected Digital Assets
Author(s):
Frankie Wallace, ,
A significant number of your digital assets, whether personal or professional, are now digital in this current age. The transfer of business practices, records, and even storefronts from a mostly physical world to a digital … Read more
Cyber Preparedness
Top 10 Cybersecurity Risks For 2019
Author(s):
Duncan Kingori, ,
2019 Risks Cybersecurity reports by Cisco show that thirty-one percent of organizations have at some point have encountered cyber-attacks on their operations technology. Cybersecurity breaches are no longer news. It is a topic that is finally … Read more