Understanding the Tech
Fingerprint Scanners: How Do They Work?
Author(s):
Zehra Ali, ,
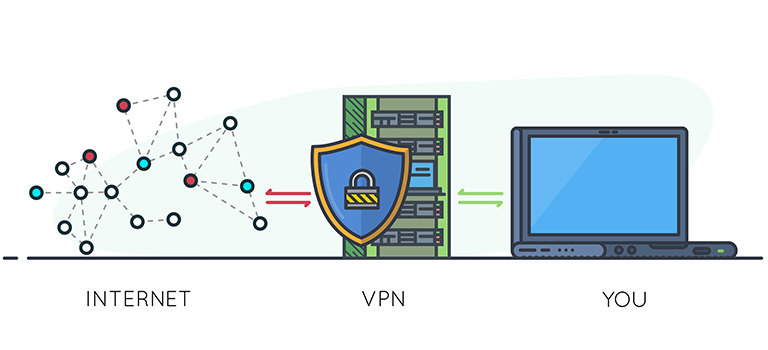
We are under the attack of many assailants. Malicious actors can harm us in so many ways that we cannot even fathom it. The most common tactic they use is by stealing someone’s identification and … Read more