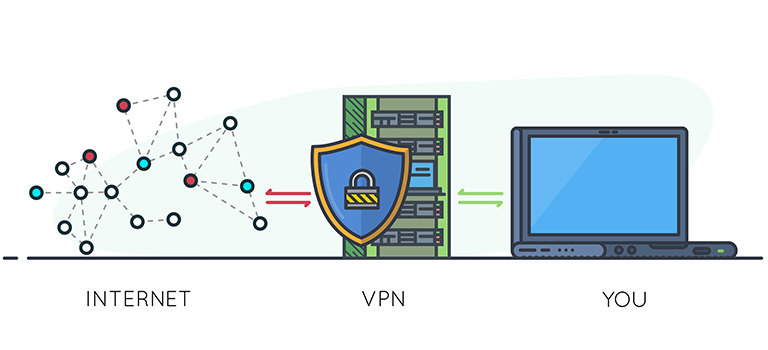
In the present era, an individual’s privacy solely depends on internet security. Your banking details, your pictures, and other sensitive information are available on different channels such as social media accounts, websites, and other online platforms. Therefore, the usage of VPN has increased drastically. But are you sure your VPN is working correctly?
If not, then you might be at risk. If you are using a weak or vulnerable VPN, then you are directly putting your data into a much worse condition.
What’s Riskier?
Fortunately, most of us understand the need for online safety and privacy due to the recent surge of cyber-attacks. However, there are still many people who do not care about internet privacy and neglect the necessary security measures they should be following.
Even if people are following basic privacy measures, they forget to update their firewalls, or they might go for a wrong VPN.
Some people want to invest less, or they want to have a free VPN which put them at more risk. However, some people remain prone to privacy theft when they are using a paid VPN. Free VPNs are considered riskier because “free” always attracts cyber goons who exploit the naivety of people. But it is not impossible to find a free or cheap VPN without any vulnerability.
DNS Leak
DNS leaks expose your online activity and IP address when you are behind a VPN service. This leak occurs due to various causes, but a reputable VPN service makes sure that all the DNS requests go through the anonymous VPN DNS server instead of the ISP DNS.
IP Leak
IP leak is the revelation of real your IP address and location when you are using a tool – such as VPN, or Tor, for IP obscuring. In addition to various small issues, the IP leak happens due to many other leaks.
1- WebRTC Leak
WebRTC is a browser feature which enables real-time communication between two individuals. With this feature, it is possible to carry out browser-to-browser video or voice calling, P2P file sharing, and other real-time communication without additional third-party software.
Enabled WebRTC can reveal the user’s real IP address even when a VPN is connected. With a little effort, the STUN server requests fetch IP address and send it to the browser. The hidden IP mostly get exposed due to the program called JavaScript.
2- Torrent IP Leak
Torrent IP leak happens when a user is torrenting via a VPN connection. Sometimes, a torrent client reveals the user’s real IP address. This leak often occurs due to the torrent client setting such as the enabled DHT and PEX features or the sometimes due to split tunneling feature of VPN.
Tactics to Reduce Risky VPN
Instead of going to a VPN guide where you directly get the names of best VPN providers, you should search for a reputable VPN yourself. The VPN recommendations are made so that users might have a clear idea of what they are going to choose. Moreover, it informs them which VPNs are reliable and which are not. However, it might be hard to figure out which one is the “right” one. Therefore, keep some things in mind:
1- Analyze the Reputation
The question-answer platforms such as Reddit and Quora have some genuine reviews and user experiences. These platforms – especially Reddit – maintain authenticity, and that’s why many experts are also involved in these communities.
Through this process, you can exactly understand the loopholes of VPN service you are searching. If you are a company owner or you are planning to get a VPN for large-scale, then you can also hire an IT consultant to help you out.
2- Discover Your Need
Your need is the most important thing when you are going for a VPN. For instance, there are many VPN protocols, and each one has a different purpose. SSTP is best for the security, but it is not fast. PPTP is good for streaming and basic web browsing, but it has security loopholes. IKEv2 is for mobile users.
Also, some people want a VPN for a specific purpose, such as Netflix streaming and torrenting. However, very few VPNs work with Netflix unblocking. If you are not sure about the VPN qualities, you can go for a comparison review, such as NordVPN vs. CyberGhost review, through which you can better understand the VPN qualities.
3- Factor in the Cost
It is evident that a free service can never run without any profit or gain. Therefore, in such case, a VPN is recouping the cost in other ways. These techniques could be the sale of your data to a marketing organization. Additionally, a free service could be a hacker’s trick to take advantage of your sensitive data.
4- Go for a Full-Scale VPN
VPN extensions can be risky because of the basic encryption and limited features. However, the full-scale VPN software improves the service with advanced features such as DNS leak protection or IPv6 leak protection. Because of complete focus, there are lots of options for VPN services as well as high-level encryption.
Tags: Cybersecurity, Data, data breach, Data Security, Hacking, Privacy, social engineering, Storage, Torrenting, VPN