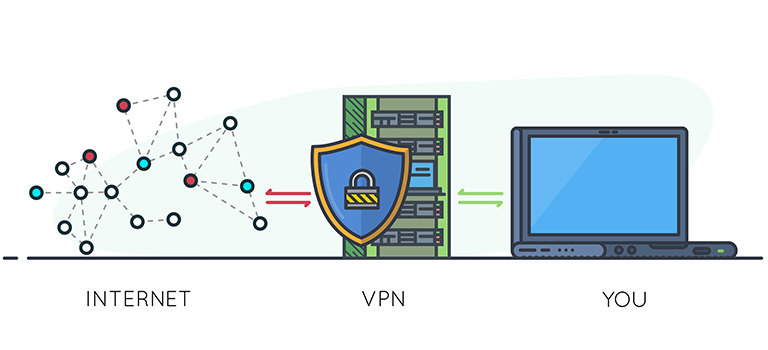
Is Online Shopping Safe? 6 Risks on E-Commerce Platforms
Author(s):
Leo Corado, Freelancer, SurfShark
E-commerce is a rapidly growing sector, expected to see over 8 trillion sales globally by 2026. With such bountiful rewards, it’s no surprise that scammers and hackers jump on the opportunity to steal funds and … Read more