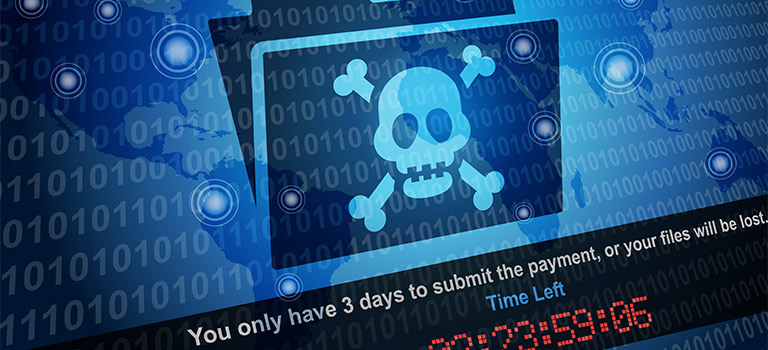
Cyber Preparedness, Understanding the Threat
Data Breaches: Having a Plan of Action
Author(s):
Frankie Wallace, ,
If you have been running your business for a while, you have likely read plenty of resources that tell you how you can protect your corporate and customer information against the potential of a data breach. As technology evolves, so do the threats that we face every day; therefore, it is important to remain protected. … Read more