Hacking
Security and Hacking Issues with Metaverse
Author(s):
Karen Austin, CEO, United States Cybersecurity Magazine
All technology has its own advantages and disadvantages, and virtual reality technologies are no different. Metaverse, the latest in virtual reality, may seem like it’s only good, but there are several security concerns that should … Read more
The Cybersecurity Industry
Cybersecurity Acronyms – A Practical Glossary
Author(s):
Lauren Abshire, Director of Content Strategy, United States Cybersecurity Magazine
Whether you are a cybersecurity professional, an end-user, just starting in cybersecurity or interested in the field, this cybersecurity acronym practical glossary is for everyone. Cybersecurity acronyms can be confusing, especially with some acronyms having … Read more
Reducing Risk
Emergency Actions After Hacking
Author(s):
Isabell Gaylord, ,
Hacking has become ubiquitous on the internet. With even major companies like Evernote getting hacked, it’s not hard to imagine that you, an individual, could also get hacked. The experience is actually quite common, though … Read more
Cybersecurity & The Modern World
What Bitcoin Needs to Become a True Global Currency
Author(s):
Frankie Wallace, ,
The popularity of bitcoin is connected with being able to purchase things across the world without changing currency, as well as being able to stay anonymous and do business without interference from government agencies. Even … Read more
Understanding the Threat
Cybercriminals in Movies and TV Shows
Author(s):
Frankie Wallace, ,
Hollywood has long held a certain image of cybercriminals. What they look like, how they commit their crimes, and their motivations. However, like many things in Hollywood, the portrayal of hackers and cybercrime in general … Read more
Cybersecurity’s Human Element
Mental Health and Cybersecurity
Author(s):
Frankie Wallace, ,
Strong cybersecurity is vital, and the cybersecurity industry is evolving at a rapid pace. Still, even as more and more companies embrace cybersecurity professionals, a key aspect of this field remains overlooked: mental health. You … Read more
Cyber and Electronic Warfare
Cyber Warfare: Modern Front-lines
Author(s):
Caleb Townsend, Staff Writer, United States Cybersecurity Magazine
Cyber Warfare is a broad term that defines a nation state sanctioned attack on a computer system of another country. One accomplishes this by means of hacking, computer viruses, and the like. Cyber Warfare: First … Read more
Reducing Risk
Social Media Platforms are Vulnerable to Hackers
Author(s):
Frankie Wallace, ,
Did you know that security concerns are turning people away from social media platforms? They are aware that hackers are obtaining users’ personal data through the most commonly visited media sites. If you are on … Read more
Securing the Network
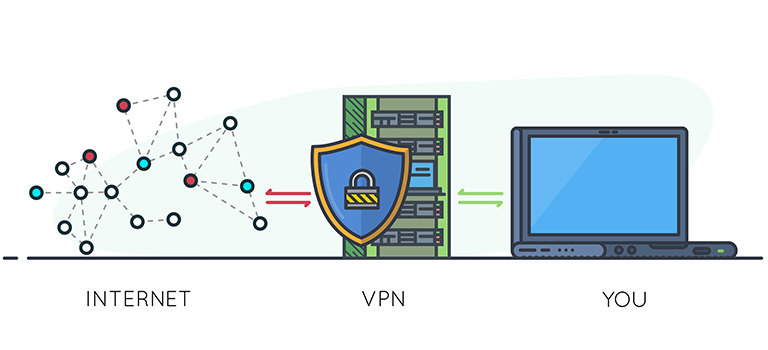
A Weak VPN Could Be More Destructive Than No VPN
Author(s):
Zehra Ali, ,
In the present era, an individual’s privacy solely depends on internet security. Your banking details, your pictures, and other sensitive information are available on different channels such as social media accounts, websites, and other online … Read more