Cybersecurity and Your Business
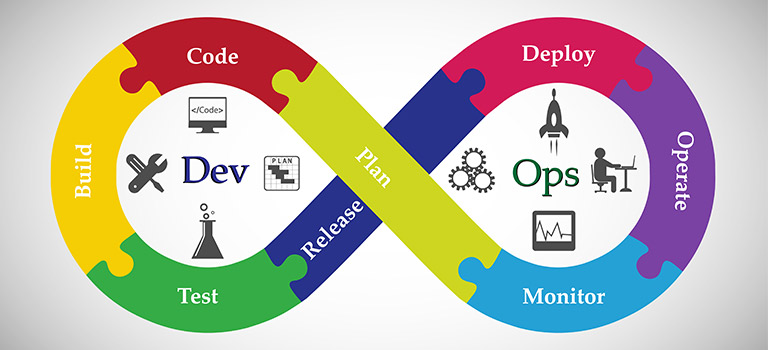
DevOps Market: Novel Approaches & Products
Author(s):
Pratik Gundawar, ,
How to Bring a Boom to the DevOps Market With competitive pressure increasing drastically and the digital economy progressing considerably, enterprises need to figure out new ways to plan, develop, and add value. Therefore, to … Read more